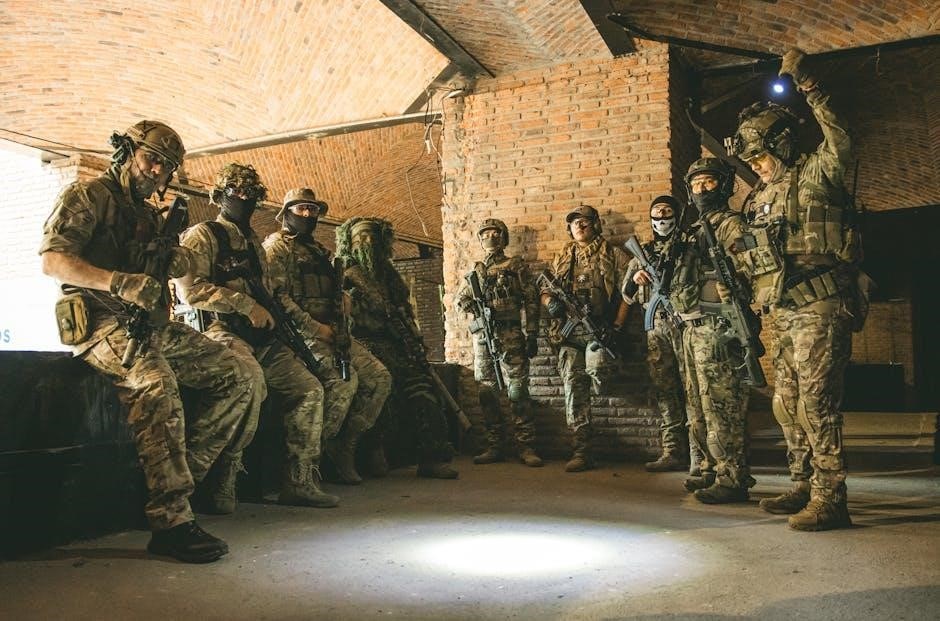
SWAT room clearing involves methodical techniques for safely neutralizing threats in confined spaces, utilizing dynamic entry and coordinated team movements.
Troubleshooting Bluetooth issues, like connection failures or interruptions, often requires checking device pairing, range, battery levels, and driver functionality.
Automated Windows troubleshooters, accessible via Settings or the Get Help app, can diagnose and resolve common Bluetooth problems efficiently.
Ensuring Bluetooth is enabled via Quick Settings and verifying the Bluetooth Support Service is running are crucial initial troubleshooting steps.
Historical Development of Room Clearing
Early room clearing techniques evolved from military close-quarters battle (CQB) doctrines, initially focused on minimizing casualties during urban warfare. The 1970s saw the rise of SWAT teams responding to increased barricaded suspect and hostage situations, demanding specialized tactical approaches.
Initial methods were often reactive and improvised, lacking standardized training. As incidents grew in complexity, the need for systematic procedures became apparent. Troubleshooting Bluetooth connectivity issues, mirroring this evolution, began with basic checks – device power, pairing – before progressing to software diagnostics.
The development of formalized room clearing tactics paralleled advancements in equipment and training, influenced by lessons learned from real-world operations. Like addressing Bluetooth errors through Windows troubleshooters, these tactics became increasingly refined and proactive.
Core Principles of Dynamic Entry
Dynamic entry prioritizes speed, surprise, and overwhelming force to rapidly neutralize threats and gain control of a room. Key principles include simultaneous entry, independent movement within the team, and establishing dominant positioning. Like troubleshooting Bluetooth connections, a systematic approach is vital.
Effective communication is paramount, utilizing clear signals and concise commands to maintain team cohesion. Thorough pre-entry planning, including intelligence gathering and rehearsal, minimizes risk. Addressing Bluetooth failures requires similar preparation – checking device compatibility and settings;
Maintaining situational awareness and adapting to unexpected circumstances are crucial for success. Just as Windows troubleshooters offer diagnostic tests, dynamic entry demands constant assessment and adjustment.

Understanding Room Geometry and Threats
Analyzing room layouts, potential cover, and likely threat positions is critical for safe and effective room clearing, similar to diagnosing Bluetooth issues.
Common Room Configurations
Room layouts significantly impact tactical approaches. Common configurations include rectangular rooms, often presenting clear lines of sight but also predictable engagement zones. L-shaped rooms create natural funnels and potential ambush points, demanding cautious advancement. Square rooms offer limited maneuverability and require precise team positioning. Rooms with multiple entry points necessitate securing each access point simultaneously. Understanding these geometries, much like troubleshooting Bluetooth connectivity, is fundamental. Identifying furniture placement, potential cover, and chokepoints within each configuration allows for proactive threat assessment and the development of effective clearing strategies. Recognizing these patterns enhances team safety and operational success.
Identifying Potential Threats & Cover
Threat identification begins with assessing potential hiding spots – behind furniture, doors, or within shadows. Recognizing individuals as potential threats requires observing body language and assessing for weapons. Simultaneously, identifying available cover for the team is crucial; solid walls, sturdy furniture, and even overturned objects can provide protection. Much like diagnosing Bluetooth issues, a systematic approach is vital. Prioritizing threats based on proximity and capability informs tactical decisions. Effective communication regarding threat locations and available cover ensures team cohesion and minimizes risk during dynamic entry and room clearing operations.
Threat Assessment Protocols
SWAT threat assessment protocols prioritize rapid evaluation of individuals encountered during room clearing. This involves categorizing subjects based on observed behaviors – compliant, resistive, or actively hostile. Similar to running Windows troubleshooters, a structured process is essential. Factors considered include visible weapons, verbal commands, and physical posture. Teams utilize a tiered response system, adjusting force levels accordingly. Constant re-assessment is critical, as a subject’s demeanor can change rapidly. Clear communication of threat levels – using standardized terminology – ensures all team members operate with a shared understanding of the situation and potential dangers.

Individual Movement Techniques
SWAT operators employ techniques like “slicing the pie” for cautious entry, limited penetration for controlled access, and controlled breaching for swift, decisive action.
Slicing the Pie
Slicing the pie is a fundamental technique for systematically exposing angles within a room before full entry. The operator incrementally reveals portions of the interior, minimizing exposure while maximizing information gathering. This methodical approach involves moving along walls, gradually widening the visible area, akin to cutting slices from a pie.
It allows for early threat identification and assessment, reducing the risk of surprise encounters. Proper execution requires maintaining a low profile, utilizing cover effectively, and communicating observations to the team. Troubleshooting connectivity issues, like Bluetooth problems, demands similar methodical steps – checking settings, drivers, and service status – mirroring the pie-slicing approach to isolate the root cause.
Limited Penetration Techniques
Limited penetration involves cautiously entering a room to a pre-determined “fatal funnel” or point of domination, establishing a secure foothold before committing the full team. This tactic prioritizes controlled engagement and minimizes exposure during the initial phase of entry. Operators utilize quick, decisive movements, immediately establishing visual contact and assessing immediate threats.
Similar to diagnosing Bluetooth connection failures – running automated troubleshooters or checking device settings – limited penetration is a diagnostic step in room clearing. It allows for a rapid assessment of the environment before fully committing resources, much like isolating the source of a technical issue.
Controlled Breaching Methods
Controlled breaching focuses on creating deliberate access points while minimizing structural damage and maximizing operator safety. Techniques range from mechanical options – utilizing Halligan tools or rams – to ballistic breaching with specialized rounds. Each method requires careful assessment of door construction, locking mechanisms, and potential threats behind the barrier.
Like troubleshooting Bluetooth issues by checking services.msc for the Bluetooth Support Service, controlled breaching demands a systematic approach. It’s about diagnosing the ‘barrier’ and applying the appropriate ‘solution’ – a precise, calculated action – to gain access, mirroring the methodical nature of technical problem-solving.

Team Formations and Communication
SWAT teams employ formations like diamond or file, prioritizing coverage and communication during entries. Clear signals, both radio and hand gestures, are vital for coordination.
Similar to ensuring Bluetooth is enabled via Quick Settings, clear communication is a foundational element for successful team operations.
Diamond Formation
The Diamond Formation is a versatile SWAT tactic, offering 360-degree security and adaptability. The point officer leads, followed by two flank officers positioned at angles, and a rear guard providing overwatch. This configuration excels in methodical clearing, allowing for focused threat assessment and controlled movement through hallways or rooms.
Effective communication, much like ensuring a stable Bluetooth connection, is paramount. Team members must relay observations and intentions clearly. The formation’s strength lies in its ability to quickly react to threats from any direction, providing overlapping fields of fire and maximizing team survivability. It’s often used when the threat level is uncertain.
File Formation
The File Formation, also known as a single-file line, prioritizes speed and maneuverability in narrow corridors. The lead officer identifies immediate threats, while trailing officers provide rear security and overlapping fire. This formation is ideal for quickly moving through hallways or doorways where a wider formation would be impractical.
Similar to troubleshooting a disrupted Bluetooth connection, maintaining spacing and communication is vital. Officers must stay close enough to provide support but far enough to avoid entanglement. While offering rapid entry, the File Formation presents limited peripheral vision, demanding heightened awareness and reliance on verbal cues.
Communication Protocols (Radio & Hand Signals)
Effective communication is paramount during room clearing operations. Standardized radio protocols ensure clear, concise transmissions, minimizing ambiguity. Hand signals supplement radio communication, providing silent cues for movement, threat identification, and immediate actions. Like resolving a Bluetooth pairing issue, clear signals are essential.
Common hand signals include directions (left, right, forward), numbers for personnel counting, and signals for “clear” or “threat.” Radio brevity codes streamline information exchange. Regular training reinforces these protocols, fostering seamless coordination and reducing the risk of miscommunication, similar to running Windows diagnostics.

Breaching Techniques
Breaching involves creating access points, utilizing mechanical, ballistic, or explosive methods, demanding careful planning and execution for safe, rapid entry.
Like fixing a Bluetooth service, proper technique is vital.
Mechanical Breaching
Mechanical breaching employs non-explosive tools to overcome physical security measures. Halligan bars, rams, and pry bars are commonly used to force doors, windows, and other barriers. This method prioritizes controlled force, minimizing collateral damage and preserving potential evidence. Operators must understand door construction and locking mechanisms to effectively apply force. Troubleshooting a stubborn lock is similar to diagnosing a Bluetooth connection issue – methodical assessment is key.
Proper technique reduces risk to both the breaching team and any occupants. Careful consideration of the door frame’s integrity and potential for structural failure is essential. Like running a Windows troubleshooter, a systematic approach increases success.
Ballistic Breaching
Ballistic breaching utilizes firearms to defeat door locks and hinges, offering a rapid entry option when mechanical methods are insufficient. Specialized shotgun rounds, designed to destroy locking hardware, are typically employed. This technique demands precise shot placement and a thorough understanding of ballistics. Like addressing a failing Bluetooth connection, accurate diagnosis – in this case, target assessment – is crucial.
Safety protocols are paramount, requiring strict adherence to firing lanes and backstop considerations. Operators must mitigate the risk of over-penetration and collateral damage. Running a Windows diagnostic tool parallels the pre-breaching assessment, ensuring optimal functionality.
Explosive Breaching (Overview & Safety)
Explosive breaching, the most forceful entry method, employs shaped charges or breaching shotguns to overcome substantial obstacles. It’s reserved for high-risk scenarios where speed and complete structural failure are necessary. Like resolving complex Bluetooth issues, explosive breaching requires specialized training and meticulous planning. Safety is the absolute priority, demanding strict adherence to established protocols.
Operators must consider collateral damage, potential injuries, and the structural integrity of the building. Pre-breach reconnaissance, similar to running a Windows troubleshooter, identifies potential hazards. Detailed post-breach procedures, including a thorough assessment, are essential.

Use of Force Continuum in Room Clearing
SWAT teams employ a graduated force model, starting with de-escalation and escalating only as needed, mirroring Bluetooth troubleshooting steps.
De-escalation Tactics
De-escalation prioritizes resolving situations without resorting to force. This begins with clear verbal commands, attempting to establish communication and assess the subject’s intent. Teams utilize a calm, authoritative tone, avoiding aggressive postures. SWAT operators may employ tactical repositioning to create distance and reduce perceived threat levels, similar to checking Bluetooth device range.
Showing empathy and actively listening can sometimes diffuse tension. However, operators must remain vigilant, constantly evaluating the subject’s behavior for signs of escalation. Recognizing pre-attack indicators is crucial, as is maintaining situational awareness. If de-escalation fails, the team prepares to transition to higher levels of force, always justified by the threat presented.
Levels of Force Application
Force application in SWAT room clearing adheres to a continuum, escalating only as necessary to neutralize the threat. Initial levels involve verbal commands and displays of force – weapon presentation – mirroring the initial checks when troubleshooting Bluetooth connections. If these fail, operators may employ less-lethal options like pepper spray or tasers.
Deadly force is reserved as a last resort, justified only when there’s an imminent threat of death or serious bodily injury to operators or others. Each level requires careful consideration and documentation, ensuring proportionality and legal defensibility. Constant assessment of the situation dictates the appropriate response, similar to diagnosing Bluetooth service issues.
Post-Engagement Procedures
Post-engagement protocols are critical following a room clearing operation. Immediate actions include securing the scene, rendering aid to any injured individuals – both operators and subjects – and establishing a perimeter. Thorough evidence preservation is paramount, mirroring the importance of documenting troubleshooting steps for Bluetooth issues.
A detailed debriefing follows, analyzing the operation’s effectiveness and identifying areas for improvement. This includes completing after-action reports and addressing any legal considerations. Like running diagnostics with the Get Help app, a comprehensive review ensures future operational success and accountability.
Equipment and Gear for Room Clearing

Essential gear includes weapon systems, ballistic vests, helmets, and specialized breaching tools like rams and Halligan bars, mirroring Bluetooth device needs.
Weapon Systems & Accessories
SWAT operators utilize a range of weapon systems tailored for close-quarters combat, prioritizing stopping power and maneuverability. Carbines, often with optics and foregrips, are primary weapons, alongside shotguns for breaching and room domination.
Accessories are critical; suppressors reduce sound signature, while weapon-mounted lights enhance visibility in low-light conditions. Laser aiming modules improve accuracy, and specialized ammunition types offer varied tactical advantages.
Maintaining weapon functionality, similar to Bluetooth troubleshooting, requires regular maintenance and ensuring proper operation of all attached devices. Red dot sights and tactical slings are also common additions.
Protective Gear (Ballistic Vests, Helmets)
SWAT operators rely heavily on protective gear to mitigate risks during dynamic entries and engagements. Ballistic vests, rated for specific threat levels, are fundamental, safeguarding against handgun and rifle rounds. Helmets, often equipped with visors and mounting rails, protect against head trauma and fragmentation.
Beyond vests and helmets, operators utilize eye protection, gloves, and groin protection. Similar to resolving Bluetooth connectivity issues, proper fit and functionality of gear are paramount. Regular inspection ensures gear remains in optimal condition, ready for deployment.
Specialized Tools (Rams, Halligan Tools)
SWAT teams employ specialized tools to overcome physical security measures during room clearing operations. Rams, both manual and hydraulic, deliver focused force to breach doors and obstacles. Halligan tools, versatile pry bars, combine prying, spreading, and punching capabilities for forced entry.
Similar to troubleshooting Bluetooth device connections, selecting the appropriate tool for the task is crucial. Bolt cutters, shotguns with breaching rounds, and other implements expand breaching options. Proper training and maintenance ensure effective and safe tool utilization, minimizing risk during dynamic entries.

Dealing with Specific Room Clearing Scenarios
SWAT teams adapt tactics for hostage situations, barricaded subjects, and multiple threats, prioritizing safety and utilizing specialized protocols for resolution.
Hostage Situations
Hostage rescue demands a cautious, intelligence-driven approach. Initial priorities involve establishing communication with the suspect, gathering information about the number of hostages, their condition, and the layout of the location. SWAT teams employ layered tactics, potentially including perimeter control, negotiation, and observation before considering dynamic entry.
Dynamic entry in hostage scenarios is reserved for situations where lives are in imminent danger. Teams utilize coordinated movements, employing flashbangs and less-lethal options when feasible. Post-engagement procedures focus on securing the scene, providing medical aid to hostages and suspects, and preserving evidence. Troubleshooting Bluetooth connectivity isn’t relevant here, but meticulous planning is.
Barricaded Subjects
Barricaded subject incidents require prolonged containment and a phased response. The primary goal is peaceful resolution through negotiation, utilizing trained crisis negotiators to establish rapport and de-escalate the situation. Intelligence gathering is paramount – understanding the subject’s motivations, mental state, and access to weapons is crucial. SWAT teams establish a secure perimeter and utilize surveillance to monitor the subject’s movements.
Forced entry is considered only when negotiations fail or the subject poses an imminent threat to themselves or others. Teams employ controlled breaching methods, prioritizing officer safety and minimizing risk to the subject. Troubleshooting Bluetooth devices is irrelevant; focus remains on containment and de-escalation.
Multiple Threat Environments
Multiple threat scenarios demand heightened situational awareness and adaptable tactics. Teams must quickly assess the number of adversaries, their positions, and potential lines of fire. Dynamic entry protocols are modified to account for increased risk, emphasizing cross-coverage and rapid target engagement. Communication becomes critical, with clear and concise updates relayed regarding threat locations and movements.
Prioritizing immediate threats and employing coordinated fire and maneuver techniques are essential. Troubleshooting Bluetooth connectivity is entirely secondary; the focus is solely on neutralizing threats and securing the location. Teams must maintain discipline and avoid tunnel vision, constantly scanning for emerging dangers.

Post-Incident Procedures & Documentation
Following a room clearing operation, meticulous evidence preservation, detailed debriefings, and comprehensive after-action reports are vital for legal and tactical review.
Evidence Preservation
Maintaining a strict chain of custody for all evidence recovered during a room clearing operation is paramount. This includes documenting the precise location of items, photographing them in situ before disturbance, and carefully packaging them to prevent contamination. Any potential evidence – weapons, casings, fingerprints, trace materials – must be secured and logged meticulously.
Troubleshooting connection issues with Bluetooth devices, as encountered with peripherals, mirrors the need for careful documentation; similarly, any alterations to the scene must be recorded. Windows troubleshooters, while helpful for technical issues, don’t replace thorough evidence handling. Post-incident reports should detail all preservation efforts.
Debriefing and After-Action Reports
Comprehensive debriefing sessions are critical post-operation, allowing team members to articulate successes, identify failures, and analyze tactical decisions made during the room clearing. These discussions should be candid and focus on improving future performance.
After-action reports, building upon debriefing insights, provide a formal, documented account of the entire event. Like resolving Bluetooth connectivity issues – requiring systematic checks – these reports detail every phase, from initial intelligence to final resolution. Windows-based documentation systems can aid in report creation, ensuring clarity and accessibility.
Legal Considerations
SWAT operations are subject to stringent legal scrutiny, demanding adherence to constitutional rights and established use-of-force policies. Documentation, mirroring the meticulous troubleshooting of Bluetooth device connections, is paramount. Every action must be justifiable and proportionate to the perceived threat.
Post-incident reviews, similar to running Windows diagnostics, must assess compliance with legal standards. Evidence preservation, detailed reporting, and transparent investigations are essential to mitigate legal challenges. Failure to adhere to these principles can result in civil lawsuits or criminal charges, emphasizing the need for rigorous training and adherence to protocol.